Table of Content
Once a buzzword, the Internet of Things (IoT) has become indispensable to our personal and business lives. It is fantastic to see IoT making great strides everywhere, from smart homes and wearables to AI-driven supply chain robotics and smart irrigation.
Therefore, it is unsurprising that today's customers want IoT products to be feature-rich, high-quality, secure, and frequently updated. The IoT market is becoming rather mature.
Businesses that want to capitalize on consumers' needs must reevaluate their plans for IoT product development with great objectivity and dedication. That is the nature of how things roll in the IoT ecosystem.
IoT - a three-dimensional technology stack
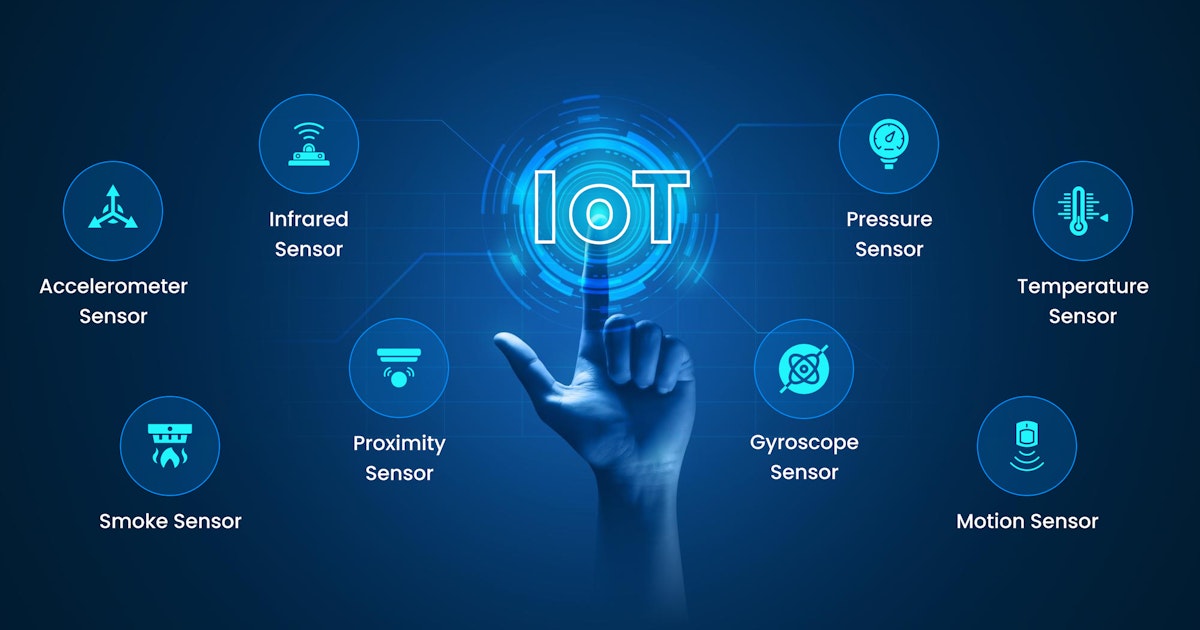
Working in IoT requires one to know about hardware, software, and firmware. While hardware is the durable equipment, people often confuse software and firmware development in IoT. However, they cannot be more different!
Embedded hardware and firmware are critical components of your smart IoT devices. They power your connected products and IoT systems, and enable edge functionality, smart operations, data collection, and drivers. Device-to-cloud and device-to-app connectivity use wired/wireless interfaces, updates, and security.
On the other hand, software runs on top of the operating system with no direct correlation with hardware. Firmware is low-level software, standing between the hardware and operating system. In this guide, we will learn everything there is to know about IoT firmware development and integration.
IoT: A phenomenon that cannot be ignored
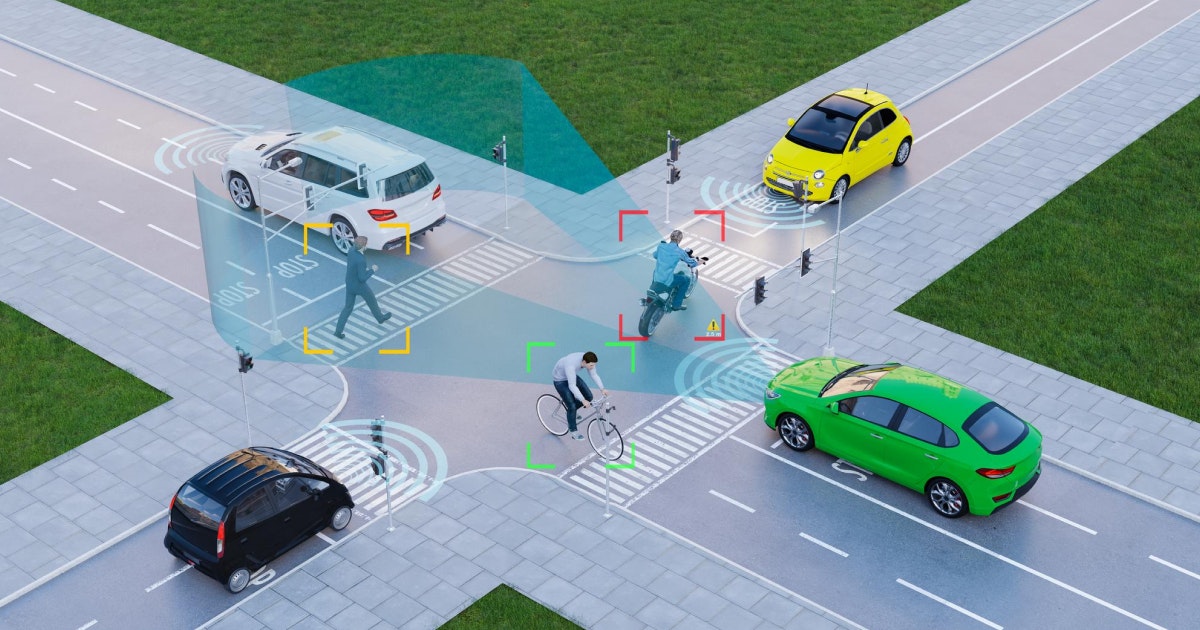
IoT is everywhere - from switching on your laptop and connecting it with any internet server to setting a washing machine in automatic mode to turning on the light with simple voice instructions.
Such activities are driven by the IoT firmware, which works as a remote control to navigate and operate any virtual system. However, with the increasing importance of IoT firmware, there are different threats as well.
Security has always been a matter of concern in IoT projects. Different devices such as baby monitors, security cameras, drug infusion pumps, and smart refrigerators have proven to be vulnerable to hacks.
We cannot deny smart IoT technologies make our life easier, but there cannot be room for security compromisation. This situation leads us to a detailed discussion about IoT device firmware and its consequences. But first, let us start with the basics:
What is meant by firmware development in IoT?
Firmware is that "hard" software residing in the system’s RAM where permanent memory loads the data and instructions for it. Firmware is hard because its instructions are loaded into a hardware solution for long-term performance with minor tweaks.
The main difference between software and firmware lies more in the functionality specifics. Software is a system component personalized to define new system functions that can only be executed within the hardware and software constraints.
Firmware engineers can use specific software stacks, operating systems, and different chip architectures to facilitate the circuitry, reduce the hardware size, and minimize project costs.
In simple words, IoT firmware development is not so different from building a standard software solution. Regardless of the management model or development mode used, firmware development comprises the following stages:
- Identify all the features of your IoT product, its functionality, how the data should be processed, and so on. In addition, you should know what SBC, microcontroller, and SoC your IoT product is based on. Your requirements should contain the methods and approaches for writing firmware and building features. Whatever you choose should not create discord among the other team members involved in development.
- Use the right tools and technologies - depending on your IoT product's hardware platform. For instance, various programming languages, tool kits, and integrated environments make the firmware development smooth and easy. If you make the right call, you can also benefit from bonuses such as completing the code in auto mode and highlighting the lines of the codebase.
- Use an operating system to build your firmware but you must have strong knowledge about its abilities and functionalities. It is better to know how everything works, for instance, configurations, schedules, and tasks. This will help you write a clean code without any problems.
- Leverage a reusable codebase to create new functionalities in addition to already existing components, for instance, methods, classes, libraries, and so on. This will help you save time and resources, and make the development process more efficient. At the end of the day, you want the development team to carry out their job without any hassle. A reusable code is just efficient.
What is IoT device firmware?
The IoT device firmware is created to let the user control any IoT device as per wish. As the device runs based on numerous lines of codes (or you can consider it a set of permanent instructions), firmware is also a piece of code available in the core part of the IoT device.
This code includes significant components required to control the user instructions for the IoT device.
The three critical features of an IoT device firmware design include the following:
Dynamic and Secure Firmware Development Services
Explore Now!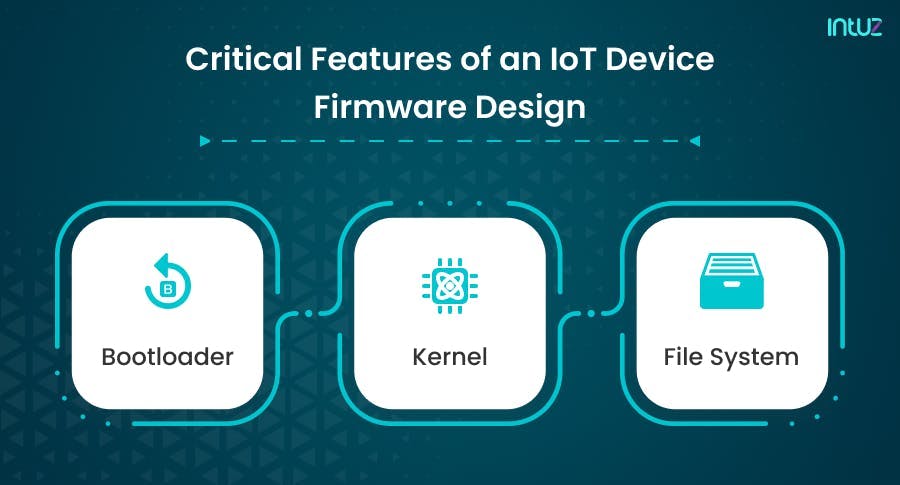
1. Bootloader
Booting in terms of a computer simply means initializing a system when it is turned on. Bootloader or bootstrap loader works to load the necessary software of the critical hardware parts and other components in the memory. A bootloader can also be called an interface between the user and IoT software for software loading.
2. Kernel
Kernel is an integral part of the operating system loaded in the IoT system. Its primary job is to align the hardware and software parts so that the IoT devices can get all the user requests without delays. It basically manages the operations of computers and hardware.
3. File system
The last step includes distinct files required to perform different jobs. As the hardware device is rebooted and the interface between software and hardware is set with the help of the two components mentioned earlier, the file system stores and sends information about other processes. It also includes web servers and IoT network services.
Types of firmware you should know about
There are many types of firmware used for IoT application production; however, there are main categories you should know about based on the level of firmware integration:
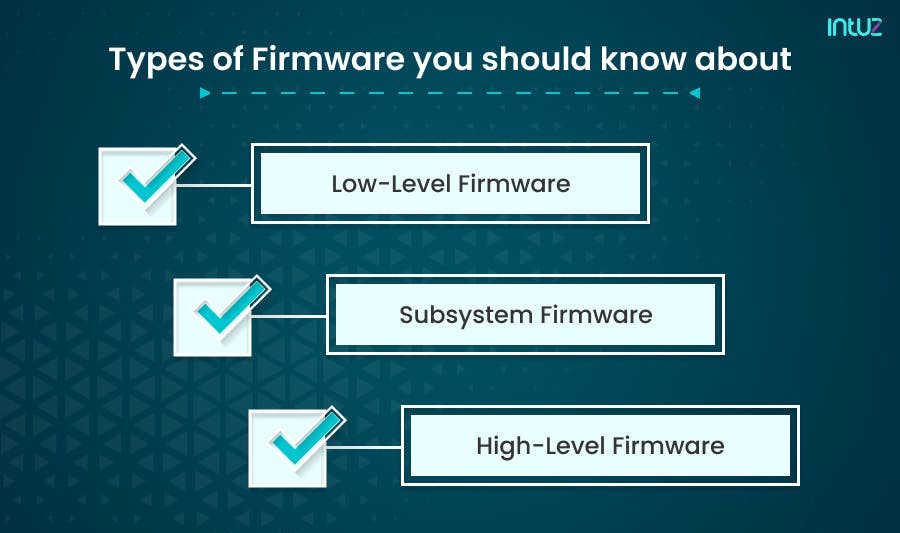
1. High-level firmware
High-level firmware allows updates and is generally more complicated than the low-level firmware. Typically, it resides on flash memory chips in a computer. It is the highest level of server or power subsystem firmware available at the repository of your choice.
2. Low-level firmware
Low-level firmware is considered an integral part of a device’s hardware. It is stored on read-only chips like ROM, which are non-volatile, therefore, cannot be updated or rewritten. Devices having low-level firmware have one-time programmable memory.
3. Subsystem firmware
The subsystem firmware comes as a part of an embedded system. It is comparable to high-level firmware because it can be updated and is complicated. A powerful example of a web server’s system is a piece of hardware that functions semi-independently from the server.
What is the process of starting an IoT device?
Ever been amazed by the IoT technology that gets your coffee ready even before you wake up? Or that water crops at appropriate intervals and per weather conditions in a full-fledged farm? Are you amazed about how the technology works? Let us understand the process of starting an IoT device:
- At first, the bootloader initiates the system setup software and is passed into the physical address of the OS kernel.
- Then, the kernel is loaded into the system from the same physical address and starts the initial process that the IoT device needs to perform.
- The bootloader expires as soon as the kernel gets loaded into the system. Then, the root file system is mounted into the kernel. A root file contains all the indexing of directories and files of a particular OS.
- Then, a ‘called program’ is generated in the kernel. That is how an IoT device gets to work in the first place.
A Guide On The Best Data Visualization Tools For IoT Applications
Access the guideHow to know what version of firmware does the IoT device have?
The most common way to find out the firmware version is to look it up on the internet. Many manufacturers often put the firmware binary file, which can be downloaded in either the “downloads” section or the “device support” section. It is also common to find out the version in different discussion forums - you can start a conversation about it.
The second method is to access the device physically. Here, you must use different hardware exploitation techniques to dump the device’s memory firmware. Depending on the IoT device and the level of protection, you can explore the hardware for binary firmware.
The third option is to sniff the OTA, i.e., get the binary code when the IoT device performs a firmware update. In the process, set up the interceptor network for the device so that the requests can be downloaded to the new firmware image, removing it from the network capture.
The last technique is to fetch the binary firmware and reverse the IoT application. This requires you to analyze an IoT device's web and mobile apps, and from there, find out the firmware version.
What is firmware security?
What is the first thing that comes to your mind when designing IoT solutions? Ease of use? Sure. Connectivity prowess? Absolutely. Security? Umm...yeah? This may surprise you, but security is often seen as an inhibitor of ease of use.
Executing IoT firmware-level security systems is essential for protecting against cyber threats. They also enable robust IoT security management and monitoring in the long run.
You see, with most computers, people interact mainly with the software and hardware, which makes it easy to believe that is all! However, computers also have a third-layer lying between the software and hardware - known as firmware.
Also known as the interface, the firmware abstracts many low-level, hardware-specific details of how the computer works, which makes it easier for a single software system or multiple software to run simultaneously.
The same philosophy is applied in the IoT ecosystem. A firmware security solution enables IoT device security and updates to be centrally managed from a cloud-based platform. Its unique security requirements mean that many conventional cybersecurity systems cannot run on them.
Top IoT security challenges to know about
Deploying a solid IoT device security nexus can be difficult for numerous reasons. When attempting to secure IoT devices, many manufacturers must deal with the following challenges:
1. Lack of reliable IoT standards
One of the main reasons why IoT devices have such a poor security game is because of the lack of IoT regulation. If you do not have security standards in place for something as volatile as IoT, the devices and their components can fail to meet even the most basic cybersecurity requirements. On the other hand, manufacturers cannot do much because they do not have the right guidance to go about it.
2. Insecure network connections
With the rise of 5G, IoT devices will increasingly leverage mobile networks and have direct connections to the public internet, which is not exactly a safe space to be in. This invariably makes the IoT devices extremely unsafe to use as they lack the protections of the enterprise security stack.
3. Use of third-party components
Supply chain vulnerabilities pose a serious risk for IoT devices as they may use components developed or distributed by third-party manufacturers or suppliers. If these components have security flaws and exploitable vulnerabilities, they may risk the IoT device’s security. No user does not want to use a flawed IoT device.
4. Poor device patching and management
IoT devices are executed under a “fire and forget” mentality. While a company’s security protocols protect traditional computers, they may not consider monitoring the Internet-connected toaster or light bulb. This eventually enhances the probability that vulnerabilities in these IoT devices remain unpatched and hence, an easy target for cyber-attackers.
Firmware security: Why is it important?
Firmware is placed below software, making it difficult to secure it properly without a dedicated solution. Firmware security is, therefore, important in many respects for IoT device manufacturers and consumers alike, including:

1. Customer confidence
Every consumer using IoT devices wants to be assured that whatever product they use is secure against cyberattacks and can safeguard their sensitive data. When manufacturers make the firmware level of IoT devices safe, they can guarantee security to their customers, which elevates their brand and boosts user satisfaction.
2. Competitive advantage
When IoT device manufacturers have proper IoT cybersecurity regulations and standards in place, especially for their firmware, marketing the IoT device’s robust security position brings with it a competitive edge, which matters a lot to the consumers.
3. Regulatory compliance
Even though this is a pipe dream, jurisdictions are actively working towards passing IoT security laws and executing strong security best practices to keep IoT-related cyberattacks at bay. There is also much focus on reducing the impact of such compliance laws on a manufacturer’s future IoT device operations.
4. Incorporated security
The unique security requirements of IoT devices mean many traditional cybersecurity solutions cannot run on them. The arrangement requires you to monitor and manage IoT devices effectively. A firmware security solution can deliver that.
5. Extended market reach
Specific industries have strict policies regarding the IoT devices that can be deployed on their networks and used for processing potentially sensitive data. Deploying firmware security can enable an IoT device manufacturer to meet these requirements and compete in compliance in the market.
6. Device security management
IoT devices, as mentioned earlier, can be challenging to monitor and manage, which makes them highly vulnerable to hackers. A firmware security solution helps stakeholders manage centrally from a cloud-based platform.
A Guide On Top 14 IoT Programming Languages
Access the guideHow to implement firmware security
There is a three-step process to protect IoT devices. The first step is to identify the potentially exploitable vulnerabilities in an IoT device. The next step is to take appropriate measures to protect IoT devices against cyber threats. One thing that is really important here is to execute IoT firmware security. This has numerous benefits, including:
- Protection against zero-day attacks
- Minimal performance impacts
- Complete firmware coverage
- Runtime protection
- Easy installation
The final stage is to keep an eye on the IoT device’s cybersecurity. You can manage updates and other security parameters for IoT devices with a proper solution - all from a cloud-based online portal. IoT devices make up 30% of all network-connected end-points, which enhances the threat surface. In any firmware, it is essential to fix bugs, add new security measures, and patch vulnerabilities.
What are Over The Air (OTA) firmware updates?
Sure, you can update the device firmware manually. However, the vast distribution of IoT-enabled devices like connected cars, pacemakers, and even coffee machines makes this manual updation impractical. That is where OTA updates enter the picture, as they help do the job remotely.
OTA firmware updates the code on connected IoT devices - regardless of the location. The update happens “over the air” in the device, which does not interfere with the underlying hardware. OTA updates are delivered through the internet network or cellular data - 4G or 5G.
The biggest benefit of OTA IoT firmware updates is that manufacturers can continually add new features, improve product behavior, and fix security bugs even if the device is placed in far-off locations.
In addition, OTA updates are cost-effective because they allow you to manage firmware across hundreds of thousands of IoT-connected devices from a centralized interface. Here are the primary benefits of OTA firmware updates:
Because the firmware stays unprotected against cyberattacks, it is easy for cybercriminals to compromise data, intrude on networks, and take control of the devices that cause disruption and harm. The bottom line is that unsecured firmware results in an unprotected IoT device.
The lack of ability to securely update the device hampers its chances of keeping cyber attackers at bay. You want a solution that keeps your IoT device protected against lack of firmware validation on the device, lack of anti-rollback mechanisms, lack of notifications of security changes, and the following:
1. Insecure coding
Hackers look for coding flaws to cause abnormal application behavior or crashes resulting in a security breach. Buffer overflows allow hackers to access devices remotely, and they can be weaponized to launch malware injection attacks or DDoS.
2. Signing a compromise
Unauthorized access to firmware-signing mechanisms or code-signing keys can enable attackers to deliver malicious updates to IoT devices that appear to be trusted but are not.
It is, therefore, essential to amp up defenses around your code-signing keys to ensure the firmware signatures are verified before the code is allowed to execute on the IoT device.
3. Unsafe software supply chain
The development of IoT devices relies heavily on the extensive use of open-source components or software supply chains. The lack of processes to safeguard the supply chain leads to employing insecure open-source components from third-party vendors with embedded vulnerabilities, which attackers find easier to exploit.
4. Ignored testing services in device production
When building and testing IoT products, developers with debugging services should not be allowed to migrate to the final production device as they offer potentially easy access to cyber hackers.
5. The outcome of unprotected firmware updates
If you update the IoT firmware without taking precautions, you will land yourself in hot soup. You are putting your consumers at risk. Data breaches are common, and hackers can launch malicious attacks remotely as soon as they break the firewall!
So you have to be careful. There are no two ways about it. Here are four examples of what insecure updates leading to an exposed firmware attack look like:
a. Smart locks
The scheduled OTA firmware update of a smart lock once comprised a corrupt version that made the updated smart locks offline. These locks, used in the hospitality sector, prevented customers from entering their rental properties. The information had to be manually updated online by the vendor. A corrupt firmware component file can take automation for a toss!
b. Pacemakers
The FDA once recommended firmware updates to resolve remote access vulnerabilities in certain pacemakers. They also said in their advisory that there was a slight risk the update may backfire, causing pacemaker failure. Unfortunately, the odds were not against the FDA, and the devices did get fried, requiring surgery to replace the pacemaker.
c. Connected cars
The research team at Tencent, a Chinese technology firm, revealed they could hack into a Tesla Model S through WiFi and remotely access the braking system. This caused much furor in the AI-driving cars community, leaving Tesla to respond by executing an essential security feature - code-signing, where any firmware written in sync with the car's components has to be digitally signed.
d. Networking gear
A developer accidentally leaked the private keys used for signing the D-link software in open-source firmware posted by the company. It is still being determined whether an external third party used the keys. However, the incident resulted in third-party investigations and hefty penalties.
How to secure IoT firmware updates
Given how quickly IoT has gained momentum, you can follow many best practices to secure IoT device firmware and reduce the impact of an update if it does not go as planned. If you are a sensible business, you must plan for everything and anything.
For starters, eliminate the storage of sensitive data such as API tokens and credentials on IoT devices. Instead, upload sensitive information to the cloud and manage the updating process without the restrictions of low-power IoT devices.
In addition, you must ensure the IoT devices are connected to only one possible attack vector - via the internet or cellular data. Limit the chances a hacker would have access to the IoT device.
As far as updating the firmware is concerned, do it regularly so that you can reduce the number of attack vectors in operating systems, applications, and firmware. It is essential to check each update.
Think of firmware as a large portion of all the tiny cogs that make the world turn, and its presence, like the IoT devices, continues to grow. Getting firmware security right in the first place is difficult, and you need experienced support to handle the entire nexus of remote devices.
Utilizing OTA firmware updates helps alleviate these problems to a great extent. OTA firmware updates are critical to IoT success as they drive the extensibility, reliability, and security of connected devices. When a bug affecting business logic is discovered, it can be updated immediately.
If new features are developed, you can push them to your IoT devices and glean more value from them. Unsurprisingly, some update mechanisms lack integrity guarantees, resulting in vulnerability to MITM and modification attacks.
The fact is that even IoT devices can use Machine2Machine authentication methods to verify an upgrade server and download a new firmware image, thus adding a layer of protection. This ensures that device updates come only from a trusted source or OEM.
Creating a unique identity and secure code signing with OTA updates ensures an unchanged update from the verified source. With the help of a secure boot, the cryptographically secure hash validation pushes integrity by checking the vulnerable patch before storing it back on the IoT device.
Top 25 IoT Development Boards In 2023 And How To Choose The Right One
Access the guideWhat is the best way to analyze firmware?
As discussed, IoT devices can be vulnerable to hacks, and the loose end is firmware. As distinct components are embedded in the firmware, the kernel can be manipulated only if bootloader access is available. That is why securing the firmware starts with analyzing it to find the loopholes.
For that, let us understand the types of file systems in IoT devices where all the information and processes are stored.
Firmware file types in IoT
- squashfs: This is a read-only file type used to store compressed files mainly to minimize data overhead.
- cramfs: This file type is used for embedded and small-footprint systems.
- JFFS2: This is a long-structured file system to handle flash memory devices.
- yaffs2: This is a long-structured file system that writes only once in each chunk with enough information and reconstructs the order of the chunk depending on recent usage.
- ext2: This is an extended file system, mainly used to make the processes faster.
Why is IoT firmware an issue?
Even after including the latest models and approaches, IoT firmware creates different problems in real-time use cases. Firstly, it is hard to secure a system primarily connected to a public network stack and readily available for access.
Also, as most IoT technologies are complex and have different testing phases, regular updates are necessary. But in this update stage, the software becomes vulnerable and prone to hacks.
What to do about it?
In the IoT industry, there is much scope for an attack, so it is always good to be protected. Besides, retrieving all the critical information becomes very costly after any cyber attack. To make the whole system protected, three fundamental steps need to be followed:
- All the core codes, including booting, system software loading, and all the updates process for both firmware and software, must be protected from public access in a computer network.
- Using a Unified Extensible Firmware Interface (UEFI) is necessary to handle large and complex industrial processes.
- Leveraging the latest technologies like ‘secure boot’ and ‘capsule update’ makes the IoT device security architecture more reliable.
UEFI is the only process that can assure a confirmed success for all the firmware-related security problems that hold back modern approaches to IoT devices on a large scale.
However, UEFI is still not becoming familiar to all developers, and it would take time to be a more powerful technology altogether. In fact, you might not need UEFI:
- If your IoT development team is not experienced enough and you do not want to mess with any type of firmware.
- If you have less than 2TB hard disk or partition.
- If you want to be able to run multiple operating systems without making any changes to the settings.
UEFI supports drive sizes up to 9 zettabytes and offers faster boot time. It has discrete driver support and runs in 64bit or 32bit mode, which helps it deliver a GUI - navigation with the mouse - easily.
Top 10 automated IoT firmware analysis and monitoring platforms
Are you looking for automated IoT firmware analysis and monitoring platforms? The one you must choose should be reliable and easy to use. Here is a list of products you can choose from before your next IoT firmware analysis and management:
1. AWS IoT Device Defender
A fully managed IoT service management firmware for auditing and monitoring IoT devices and fleet assets, AWS IoT Device Defender gathers security metrics from the connected devices and audits cloud-side configurations.
Further, it authenticates the devices and runs Machine Learning (ML) algorithms to detect anomalies. The firmware constantly monitors the operations and proactively publishes alerts in case of any security vulnerabilities. It facilitates built-in remediation and control actions to prevent the identified security issues.
Features:
- Includes automated audits on security positions and immediately reports the configurations incompliant with AWS IoT security best practices.
- Deploys rule-based and ML-based anomaly detection capabilities to monitor and assess security metrics violating the defined behavior.
- Incorporates built-in mitigation actions that instantly troubleshoot the outliers in network traffic monitoring.
- Deploys security patches and rebooting operations to fix the security gaps, vulnerabilities, and threats associated.
- To minimize operational risks, it triggers automated alarms to preferred AWS interfaces, such as Amazon CloudWatch, Amazon Simple Notification Service (SNS), AWS IoT Console, and device management.
2. Google Cloud IoT Core
The highly favored fully managed IoT firmware for establishing a convenient, secure, and well-managed connection between IoT devices, Google Cloud IoT core effortlessly fetches and retrieves data from globally distributed devices.
In addition, it develops feature-rich and easy-to-integrate applications that can smoothly function with other big data services.
The Google Cloud Architecture Framework is resilient, scalable, and reliable. The cloud topology designed best operates for hybrid cloud deployments, multi-cloud environments, and applications migrated from local to Google Cloud.
Features:
- Facilitates end-to-end solution and operation excellence for real-time IoT data gathering, processing, analyzing, and visualizing.
- Seamlessly clusters distributed IoT data into a central global system for forecasting outcomes, advanced analytics, and optimizing business.
- Runs on serverless infrastructure and automatically scales volatile requirements, reducing capital expenditures and maintenance costs.
- Supports industry-standard security protocols like MQTT and HTTP for secured and hassle-free data ingestion. Moreover, it establishes high-frequency and low-latency communication.
- Employs a smart and super responsive IoT data pipeline that proactively updates business devices with IoT Core.
3. McAfee Embedded Control (MEC)
MEC is an application-independent IoT security firmware that requires low-density computing space and costs minimal. It works on hands-off deployment infrastructure and facilitates both blocking and listing solutions for IoT devices with fewer updates.
MEC specializes in preventing unauthorized programs (applications or codes), from altering changes or damaging the authorized commercial baseline data.
Services such as POS terminals, ATMs, healthcare devices, and communication and industrial control systems predominantly employ MEC. The firmware provides 360-degree enterprise-level security covering endpoints, networks, servers, data, embedded systems, and devices.
Features:
- Encompasses McAfee Endpoint Security (ENS) that works on single agent architecture and AI-guided investigations.
- Includes ePolicy Orchestrator (ePO) security control application powered by McAfee Integrity Control (MIC), enabling automated compliance and centralized instant updates.
- Utilizes McAfee Complete Endpoint Threat Protection (CTP) to encrypt commercial baseline data and ML analysis to foster behavior-based Zero Day Intrusion Prevention.
- Automatically rolls back malicious actions through the anti-malware engine constantly upgraded by McAfee Global Threat Intelligence.
- Furnishes more significant visibility about emerging threats, streamlines operations, and performance tuning.
4. AppSealing
Powered by INKA Entworks Inc., AppSealing is a cloud-based SAAS security solution for apps and mobile IoT devices. It is entirely no-code and perfectly supports IoS, Android, and Enterprise-Grade Hybrid OS.
AppSealing safeguards from illegal data manipulation and theft. Due to its Robust Security Technology, AppSealing has been able to serve patented application protection solutions to prominent industries, specifically those with stringent compliance requirements, such as IoT, gaming, fintech and banking, eCommerce, media, healthcare, and government.
Features:
- Protects IoT apps from potential risks in runtime and with a real-time scalable threat analytics dashboard.
- Provides in-app protection without impacting performance and is easily compatible with third-party library packages.
- Runtime Application Self Protection (RASP) security features shield real-time source code, the app's integrity, and anti-debugging.
- Enables detection possibilities in vulnerable areas, such as cheat tools, memory access, network packet sniffing/spoofing, and so on.
- Uncovers and troubleshoots susceptibilities with easy-to-use integrated advanced defense solutions; also, it is highly affordable as it works on the Pay-As-You-Go (PAYG) business model.
5. Azure Sphere
Azure Sphere is a secure and comprehensive IoT platform for building, connecting, maintaining, monitoring, and protecting intelligent devices. It strives to facilitate high-value security at a low cost and with no consumption fees.
It employs a crossover embedded processor MCU core, customized high-performing Linux OS, and a cloud-based security solution. This robust configuration fosters uninterrupted and sustainable security. In addition, Azure Sphere enables interoperability between IoT platform services that make deployment convenient and streamlined.
Features:
- Over-the-air (OTA) updates seamlessly release the patches to the connected IoT devices and protect them from potential security risks.
- Azure Sphere-certified guardian modules provide end-to-end secure IoT devices and assets - from edge to cloud.
- Helps expedite the business delivery in terms of value, experience, and response to the end consumers.
- Offers myriad options of devices to create industry-specific secured IoT solutions, following business requirements, usage, and purposes.
- Protects from device spoofing through the tamper-resistant cryptographic key.
- Remotely performs immediate service updates in case of operational failure reporting.
6. Azure IoT Hub
This is undoubtedly the best-in-class IoT firmware to securely connect, manage, and monitor billions of IoT fleet assets. It facilitates serverless computing, scalable provisioning with integrated device management, and per-device authentication.
Azure IoT Hub offers a cloud-hosted back-end solution to establish reliable two-way communication between the IoT application and its assets.
The compatibility with Azure IoT Edge and complete integration with Azure Event Grid make hybrid IoT application development convenient. Azure IoT Hub supports HTTPS, AMQP, MQTT, AMQP over WebSockets, and MQTT over WebSockets protocols for connecting devices.
Features:
- 360-degree security and compliance solution with built-in Azure Defender for IoT; monitors security postures and threats with remediation.
- Automatically sends messages, commands, and notifications both in case of steady and intermittent connectivity.
- Tracks data delivery with acknowledgment receipts analyzes telemetry, and synchronizes the device management workflows.
- Speedily responds to security threats and vulnerabilities by deploying OTA updates at no extra cost.
- Allows building and deploying IoT Edge modules for data transmission between cloud and edge as per business-specific objectives.
7. Mbed OS
Powered by Arm Limited, Mbed OS is the most trusted, free, open-source operating system to develop intelligent connected products.
It incorporates all the essential features, libraries, drivers, security protocols, and connectivity stacks required for building IoT Applications. In addition, Mbed OS employs Keil RTX and RTOS APIs for real-time software execution.
The latest version, Mbed OS 6.1, operates on the componentized and layered architecture encompassing ML capabilities. It supports cloud service integrations, such as Pelion, AWS, Azure, and Google IoT on Arm Cortex-M-based hardware.
Features:
- Supports over 70+ IoT modules, cloud services, and OEM partners, improving development from prototype to production.
- Fastens the development phase keeping the source code clean, simple, easy to understand, and portable.
- Implements retargeting and boot process integration to reduce application development time, cost, and potential risks.
- Deploys Platform Security Architecture (PSA) that offers Arm Mbed TLS and Secure Partition Manager (SPM) to shield IoT devices.
- Compatible with Cellular IoT (LPWA), LoRaWAN, Thread, BLE, PoE, and Wi-Fi connectivity protocols.
8. FortiNAC
Powered by Fortinet, FortiNAC is a zero-trust network access control solution exclusively designed for IoT at the enterprise level.
It strengthens the security fabric with improved visibility, risk control, and automated responses. Also, FortiNAC scans and detects anomalies at every network endpoint and downsizes IoT threats.
It is available in FortiNAC-CA-500C, FortiNAC-CA-600C, FortiNAC-CA-700C, and FortiNAC-M-550C hardware appliances, virtual machines, and licenses.
FortiNAC's functionalities range from control and application to management servers, and it manages ports in the network from 2,000 to 25,000 - unlimited, depending upon the enterprise's needs.
Features:
- Increases visibility throughout the enterprise network by furnishing accurate profiling retrieved from multiple behavior sources.
- Implements dynamic network access control and micro-segmentation policies to expand Security Fabric's reach in variegated environments.
- Triggers a wide range of customizable automated responses to activate configuration changes instantly against IoT threats.
- Devised over the centralized architecture for hassle-free deployment and effective management with network infrastructure.
- Supports third-party network devices and reduces investigation time by direct event reporting to SIEM.
9. Microsoft Defender for IoT
An integrated, comprehensive, and agentless NDR security solution for IoT, Operational Technology (OT), and Industrial Control Systems (ICS), Microsoft Defender for IoT is specifically for IoT infrastructure.
It provides lightweight micro-agents to shield device-layer security and is interoperable with Microsoft Sentinel, Microsoft 365 Defender, and external SOC tools - the need of the hour.
The core capabilities include unauthorized device discovery, vulnerability detection, and immediate response with troubleshooting. Microsoft Defender for IoT supports 100+ protocols like EtherNet/IP, Modbus, BACnet, Siemens S7, DeltaV, IEC 61850, Yokogawa, and so on.
Features:
- Utilizes ML models, threat intelligence, and behavioral analytics to monitor illegal or abnormal activity.
- Employs agentless network monitoring to determine the underlying cause of intermittent connectivity and operational problems.
- Offers multiple deployment options such as on-site, cloud, or hybrid and perfectly supports IoT OS like Linux and RTOS.
- Publishes IoT real-time alerts across enterprise networks for proactive recovery and examining historical traffic for potential risks.
- Deploys distribution model and endpoint security with minimal impact on overall performance and extensible customization options.
10. FortiGuard Labs
A key instrument powered by Fortinet, FortiGuard Labs specializes in threat intelligence. It comprises an experienced team of data scientists, engineers, researchers, analysts, and cyber threat hunters and facilitates an annual global threat landscape and predictions that help enterprises to enforce optimal security policies.
The extensive resources include blogs, threat signals, zero-day research, threat intelligence briefs, podcasts, and FortiGuard Live Videos. FortiGuard Labs develops data-rich products in network, content, endpoint, application, and response services.
Features:
- The magnitude of visibility is directly proportional to the telemetry accumulated from 5.6M+ globally deployed IoT-connected devices.
- The data insights uncover the real-world threats concurrently available in IoT devices, endpoints, networks, and web applications.
- FortiGuard Labs devises serviceable security protection updates gathered from the innovative Fortinet Distribution Network. These updates help in enhancing the Security Fabric in real time.
- The exhaustive Zero-day research furnishes dynamic analytics and actionable intelligence on security vulnerabilities.
- The FortiGuard Labs knowledge base greatly helps enterprises address emerging threats and proactively deploy advanced defense solutions.
Over to you
IoT firmware is the engine that drives an IoT ecosystem, and its prominence will grow as the number of connected devices continues to increase. Maintaining firmware can be difficult as it encompasses everything - from security concerns to business logic. However, it enables networking among remote devices, and its challenges can be addressed by OTA updates.
We at Intuz specialize in top-of-the-line firmware development of IoT products. We create advanced user solutions for both low-level and high-level needs and purposes. Today's customers want the IoT products to be feature-rich, top quality and secure, and we strive to deliver just that!
From interconnected IoT devices with tracking software to centralized radio systems - we offer firmware development, including API utilities and BIOS settings. Besides, we can help you migrate existing device drivers to another hardware platform or operating system.